Data Security for Social Media Influencers and Creators – Best Practices and Tips for 2026
Author: Dakshit Mathur
10 minute read
A DIY social media influencer woke up one morning to a shocking reality: she had been locked out of her Instagram account, rendering six years of hard work and creativity completely inaccessible. This unexpected setback threatened her relationships with major retailers like Home Depot, Wal-Mart, and Target. She poignantly described her situation, saying, “It’s like watching your entire store burn down without insurance, feeling utterly helpless with no one to turn to for support.”
In India, a social media creator with 57 million followers was extorted $60,000 through cybercrime. Over the course of 12 months, he paid the extortionists to prevent fake copyright strikes from jeopardising his 96 Instagram pages. 95% of social media influencers lose invaluable relationships with brands as a result of security issues.(Source)
These situations occur frequently. If you’re a social media influencer and your Instagram account is your only source of income, a security breach will prevent you from accessing your account. On top of that, it may disrupt your active campaigns and stall your audience engagement, impacting your contracts, deliverables, and future payment streams built over the years.
Your Account is Your Business Framework
An Instagram social media influencer’s email and account were hacked, causing her to lose 42,000 followers after the hackers seized her accounts and demanded payment (or they would destroy everything). After not paying, she filed a police report. Two hours later, the hackers deleted her Instagram account, including her 42,000 followers.
This is the new reality: social media influencers are businesses, and one compromised password can erase years of audience building, brand development, and keepsake content. To understand social media influencer marketing, we need to see that social media profiles are not personal. They are valuable, revenue-generating assets built on engagement, reach, and community social trust that require business-level security.
Losing followers is only one part of the issue. Other losses include ongoing negotiations with brands, completed contracts awaiting product delivery, payment accounts with thousands of dollars pending, and documentation showing which brands can use your content. If a hacker changes the email or phone number linked to your account, recovery becomes impossible.
Where Data Security Actually Fails on Social Media
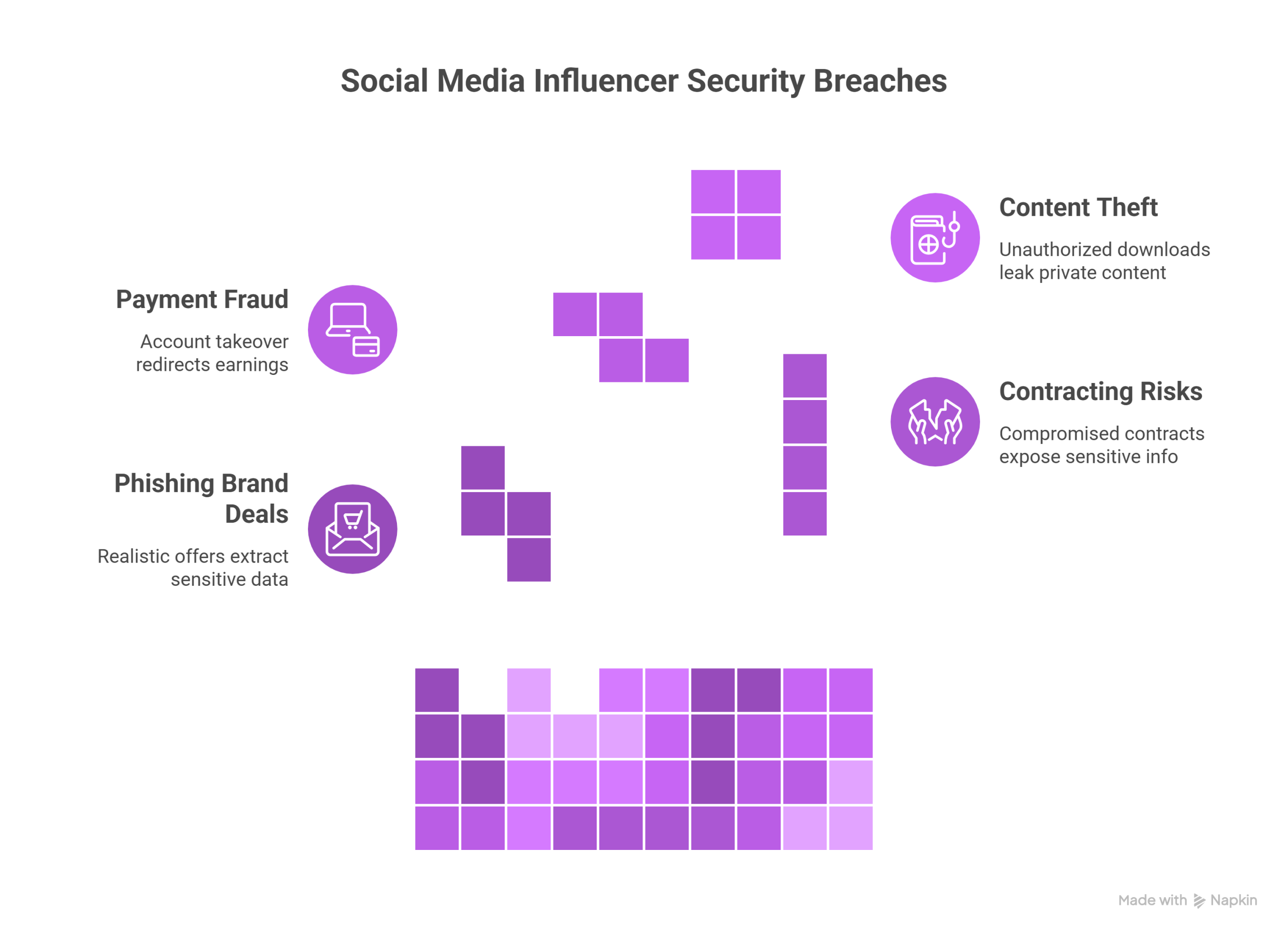
Many major security breaches occur where social media influencers conduct most transactions: finding and negotiating deals, providing and paying for content, and managing the use rights of produced content.
1. Phishing Brand Deal Scams
Attackers know how social media influencer partnerships work and send emails that appear to be legitimate brand offers, often with realistic contracts attached as PDF or ZIP files. When the target opens one of these documents, the infostealer malware silently extracts their browser passwords, session cookies, and authentication tokens.
For instance, fake companies offer partnership agreements that require social media influencers to make an upfront purchase. After the purchase, there is no further contact from the brand. Often, there are messages indicating that someone is offering to verify your account; you must click this link/submit your username and password.
Sometimes, fake talent agencies promise sponsorship for an upfront fee, using fake testimonials or websites as proof of legitimacy. According to SpyCloud researchers, in 2024, an average of 1,861 cookies were collected per malware attack. Session hijacking with a stolen cookie lets an attacker bypass both your password and two-factor authentication.
2. Contracting and Usage Rights Risk
Social media influencer contracts include content-use rights, exclusivity, unreleased campaign information, and private payment arrangements. If this documentation is improperly accessed or compromised, it becomes available to competitors and bad actors.
According to experts on contract security, the risks of social media influencer contracts include:
- Little to no detail about who owns content after a campaign has ended
- Lack of detail in the documentation regarding usage rights for brands that want to reuse content beyond the original agreed-upon date
- Exposed email negotiations regarding payment structures to unauthorized parties
- Hacked cloud account information because agreements are unsigned and, therefore, do not provide legal protection.
Well-prepared social media influencer contract templates provide a legal framework and help ensure campaigns run smoothly. However, if these contracts are stored in compromised Google Drive accounts or sent to compromised email accounts, they become worthless to third parties due to leaks.
3. Payment and Account Takeover Fraud
Payment fraud is one of the fastest-growing areas of concern facing the creator economy. However, the most serious threat is account takeover, followed by redirected payment.
Using phishing or credential stuffing to get the creator’s password, criminals can change the creator’s bank account information to one they control. When this happens, the creator’s earnings can be lost overnight.
Examples of how payment scams occur include:
- In advertising, brands fraudulently use someone else’s payment method; the person ends up having to pay the amount back weeks after it was charged.
- Creators’ earnings can be inflated by providing information that makes it seem they have more engagement than they do. This inflated value results in additional payment and return abuse.
- A person’s PayPal, Venmo, or bank account can be changed without consent once their payment information is compromised.
Criminals can also use phishing emails that appear to be legitimate business requests from various payment platforms to obtain account verification information. Hence, having a strong financial foundation and awareness matters the most for social media influencers today.
4. Theft of Delivered Content and Deliverables
Social media influencers often upload files or send attachments to brands through shared drives, email, or third-party platforms during delivery. Each handover point creates an opportunity for theft, unauthorized downloads, or the leaking of content intended to remain private until a set time.
In the case of a compromised account, a social media influencer may lose access to:
- Campaign assets downloaded before the launch date.
- Raw footage and outtakes that may be downloaded & used illegally.
- Edited deliverables that are intercepted prior to being sent to the brand.
Personal files on computers or cell phones that are backed up online may also be vulnerable to data theft.
Practical Data Security and Cyber Safety Tips for Social Media Creators
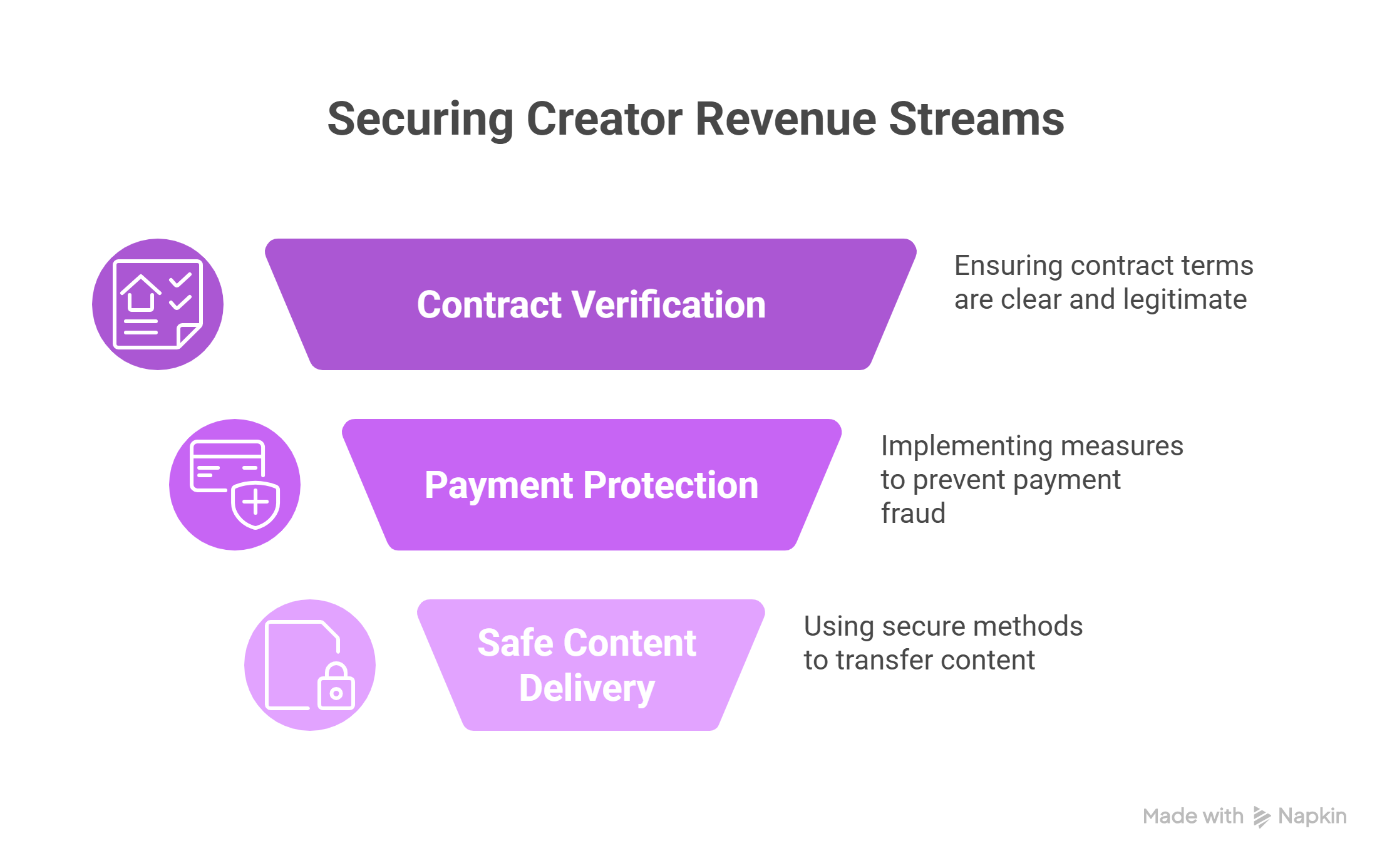
A clear, repeatable process can help secure the four main revenue streams for creators: brand deal vetting, contract verification, payment protection, and safe content delivery.
90-Second Brand Contract Security Check
Before clicking any link in an email or direct message claiming to offer a collaboration, verify that the sender’s domain matches the brand’s official website.
For example, a legitimate Nike partnership should use a @nike.com email address, not a generic one.
Check the sender’s name on LinkedIn to confirm their affiliation with the organization. Do not open attachments, such as PDFs or ZIP files, from first-time contacts. Legitimate brands will provide campaign briefs through secure portals or after an initial call.
When looking for real brand partnerships, remember that real brands will never require you to pay upfront for sample products, ask for your Instagram password for verification, expect you to respond immediately to an expired offer, or request your banking details before you sign a contract.
The most common phishing scams include fake verification badges, discount ambassador scams where you buy products upfront and never get your money back, fake agency recruitment charging fees, and copyright strike extortion demanding money. If something seems off, verify by using the contact information on the brand’s official website.
Mitigate Third-Party and AI Tools Risks
Any analytics platform, social media post scheduling tool, or AI content generation tool you connect can create a potential backdoor to your accounts. Review all requested permissions before connecting a new tool. “View and post content” is a reasonable request for a scheduling tool, but “full account access” and “change password” are not appropriate.
Verify which tools encrypt your data, where their servers are located for GDPR compliance, and whether they resell your data to third parties. A good understanding of generative AI security helps you better evaluate AI content tools, which often require sensitive permissions and access to your creative works.
Regularly audit your connected applications by visiting Instagram Settings, then Security, then Apps and Websites, and reviewing each connected app. Remove any you haven’t used in over 60 days. Repeat this process for TikTok, YouTube, Facebook, email accounts, PayPal, and Stripe.
Protect Your Contract and Usage Rights
Protect yourself against income loss by using contracts that clearly outline the amount, timing, and manner of payment, as well as the circumstances that will trigger payment for your work.
For example, “1 Instagram reel, 30-60 seconds, product demonstration format, and to be posted by March 15” provides better clarity than simply stating you’ll provide “some social media content”. Also, define revision limits and approval processes in your contracts for all deliverables.
The use of content is where many creators can get into trouble. Document in your contract the ownership of content, whether brands may use your content on their channels after it has been posted or as paid ads, the specific platforms where they may run your content, and the duration of their usage.
Also, ensure any exclusivity language that limits future opportunities with competing brands is well defined, has a specific duration, and provides reasonably equivalent compensation.
Keep all signed contracts in a password-protected cloud storage folder with two-factor authentication. Do not share contracts through standard email services, and keep local copies separate from cloud storage services.
Tighten Your Payment Security to Prevent Fraud
Invoice fraud targets creators during payments via PayPal, banks, or other payment platforms. Fraudsters compromise your accounts to steal your money, and set up payment platforms and bank accounts using email and mobile phones with authenticator apps.
Set up a separate bank account for creator revenue and a separate email address for each payment platform for all your accounts.
Enable real-time alerts for transactions over $10 and review your bank statement weekly for unusual activity. Watch for signs like login attempts from unknown locations, unexpected password reset emails, notifications that your payment account has changed, or requests to verify your account by clicking a link.
If you notice anything suspicious, change your passwords immediately on a secure device, check the destination accounts for payments, and contact the payment platform’s fraud department.
Ensure Safe File Transfer for Content Delivery
If you’re sending thousands of dollars’ worth of content, use a secure file transfer system like WeTransfer Pro or Dropbox Transfer, which lets you create password-protected, 7-day-expiration links for your clients. Provide a watermarked version for review while they wait for final payment, and send a non-watermarked version once payment is confirmed.
After you have confirmed receipt of content by the brand, delete all the links you previously shared with them to prevent their continued unauthorized access to your files.
Keep a bookmarked copy of your files in a secure, archived, and backed-up location, along with the signed contract for each project. If your files are lost, disputed, or used outside agreed-upon rights, this documentation provides evidence of what you sent and when.
Make security your competitive advantage
When an organization evaluates potential partners who demonstrate cybersecurity awareness, those partners gain greater credibility. Showing security awareness during contract negotiations signals professionalism:
- “I use two-factor authentication as well as encrypted file sharing for any file I send to you.”
- “I use password-protected cloud storage and have a record of any changes made to my contracts.”
- “I have a separate system for handling my own financial transactions, which will protect both of us.”
By having these conversations, you establish yourself as a lower-risk partner, which allows you to charge more per hour and maintain long-term working relationships.
Influencer security is not about enterprise software or technical solutions, but about protecting daily workflows that generate revenue, brand-deal vetting before clicking links, strong authentication for payment accounts, safe storage of contracts and usage rights, and encrypted content delivery.
Sustainable social media creators understand their influence lasts as long as the infrastructure that supports it. That infrastructure begins with implementing simple, consistent security practices into the way you already work. Your next brand deal depends on it.